When it comes to ensuring that our personal information and online activity remains private, VPNs and Tor are the most powerful tools you can use. Both share striking similarities, but it’s their differences that make them useful in niche situations. Whether getting around a geoblock or navigating through the dark web, you’ll need to understand which choice is right for which situation.
What Is Tor & How Does It Work?
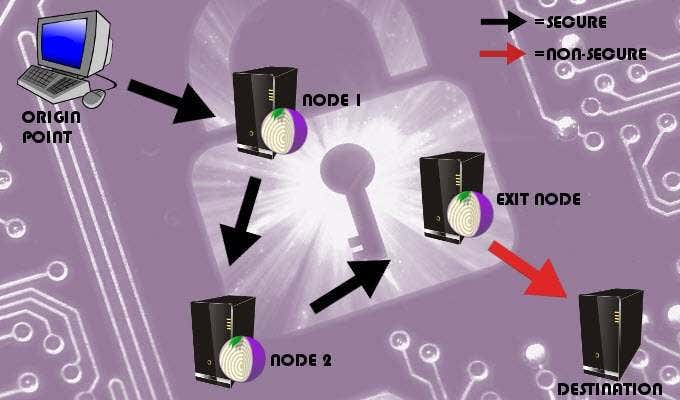
Tor, short for The Onion Router, is free software that provides a hidden traffic service, protecting your identity by encrypting your online traffic and routing it through multiple volunteer-operated nodes. Each node benefits from multi-layer encryption, allowing the network to see only the IP address of the node before and after. The exit node is also visible and the only one that can see your encrypted data. Since the nodes are operated by volunteers, anyone is free to set up an exit node. The problem with this is that a poorly setup node can harvest private information which can remain visible to hackers and spies. Tor will prevent all browsing activity from being linked back to you but anyone can see your traffic once it leaves the network. All but where it begins, that is. To keep your privacy secure, you should avoid sending private messages and other sensitive information over your connection. Tor will map a path that begins from your device, routing you through two randomly selected nodes, until finally coming to an exit node. Prior to sending out your data packet to the first node, Tor will apply three layers of encryption. The first node on the trip will remove the outermost layer, which is the layer that knows where the data packet is headed to next. The second node will repeat this process, sending your data packet to the network’s exit node. The exit node removes the final layer, revealing all of the information the data packet was carrying. To keep hackers guessing, Tor will continue to use the same three nodes for no more than 10 minutes before creating an entirely new, random route for your traffic.
The Advantages Of Tor
Tor is 100% free, making it the most cost-effective solution for your security.There are no logs or records kept within the Tor network. There are no sign-ups and you won’t have to worry about your financial information being released when using the software.Tor has no worries of ever being shut down. All nodes are scattered across the world making it virtually impossible to ever be in danger of removal. Having no main server keeps it free of attacks and raids from malicious entities and legal authorities.
What Are VPNs & How Do They Work?
A Virtual Private Network (VPN) provides end-to-end encryption from your device to a remote server in any country a server is available. While using a VPN, your IP address is hidden, making it appear as though you are accessing the internet from the location of the remote server instead of your actual location. You’ll need to choose a provider, create an account, launch the client from your device, log in, and then select the appropriate server. An appropriate server would depend on your needs. For a more secure and swift connection, a nearby server is preferred. If looking to circumvent region-blocked content, connect to a server in a different country with less restrictions. Once connected, all data will be encrypted prior to being routed through your chosen server. The data will then traverse through the tunnel to the website you’re trying to access. Your IP will be masked from the website, and in its place will be the server’s IP address, making your access completely anonymous.
The Advantages Of a VPN
All data is encrypted from origin to destination.VPNs can either slow down or speed up your connection, depending on network congestion and if your ISP throttles your bandwidth.Technical skills are not normally necessary when a VPN is concerned.A VPN can help you get around geo-blocked restrictions through IP masking. Unable to watch US Netflix while stationed in Korea? A VPN may be able to help you overcome that obstacle.
Tor vs VPN – Combining Forces
By combining both Tor and VPN, you can create a powerhouse of online security and privacy protection. There are two ways to combine a VPN and Tor; either Tor over VPN or VPN over Tor. The choice will be determined by your needs.
Tor Over VPN
A VPN connection will need to be made first before opening Tor. Doing it this way will allow the VPN to encrypt your traffic before doing your business on Tor. This will hide your Tor activity from your ISP. Your ISP will be unable to see the data being sent over Tor, even though they can still see that you’re connected to it. Since the Tor entry node isn’t able to see your real IP, it will be shown the IP of your VPN server, increasing your anonymity. Your traffic however is not encrypted once it leaves the Tor network, leaving you without protection from malicious exit nodes. You’ll still need to be very careful about sending sensitive information over your connection. Choose Tor over VPN if:
You need to hide your use of Tor from your ISP.You need to hide your traffic from your VPN provider.You won’t be sending sensitive information over your connection.
VPN Over Tor
Using this method will go in the opposite direction from Tor over VPN. You’ll need to connect to the Tor network first before logging into your VPN. This will require that you are more technically sound, as you’ll need to configure your VPN client to work with Tor. Tor’s exit node reroutes your traffic to your VPN server, eliminating the risk of malicious exit nodes. This happens because your traffic is decrypted after it leaves the Tor network. The entry node will still be able to see your real IP, but your VPN will only see the exit node’s address. This hides the fact you’re using a VPN from your ISP but they can see that you’re on the Tor network. This setup will make it easier to bypass geo-blocking, allowing you to access some Tor nodes you were originally unable. Choose VPN over Tor if:
You want to protect your online connection against malicious exit nodes.You need to hide your VPN use from your ISP.You plan to transmit sensitive information over your connection.You need to bypass geoblocks.